DevOps Assistant Agent
Provision access, enforce policy, and keep permissions current — without the manual overhead
Stop clicking through admin consoles every time someone needs access to a system. This agent handles identity and access management for your internal employees — provisioning the right access levels, enforcing policy, and reviewing permissions on a recurring basis — so your engineers spend less time on admin and your access controls stay accurate.
The result: 30+ min saved per access request, and 100% recurring access reviews with zero manual effort.
What it does
- Provision employee access to cloud and internal systems
- Enforce policy-based permission levels per role
- Review existing access rights on a recurring schedule
Tools & Integrations
Opens Abundly with a starter prompt — our AI helps you tailor it to your business
The Challenge
Access management sounds simple until you're the person who actually has to do it.
A new employee starts. Someone on the DevOps team gets a message: set up access for this person across three cloud environments, two internal tools, and a handful of shared resources. The engineer opens the cloud provider console, navigates to IAM, creates the right roles with the right scopes, double-checks the policy documentation to confirm which permission level this role should have, and repeats the process for each system. For one person, that's thirty minutes of careful clicking. For a batch of five new hires in the same week, it's half a day of admin work that pulls an engineer away from infrastructure they were supposed to be building. The provisioning itself is only half the problem. Access rights are rarely static. People change roles, move teams, take on new responsibilities, or leave the company — and their permissions should change with them. In practice, they don't. Old access lingers. Permissions accumulate. Nobody has time to run a proper review, so the audit that should happen quarterly gets pushed to next month, then the month after that.
When access management is manual, mistakes are inevitable. An overly broad permission set on a service account goes unnoticed. A former team member still has production access three months after switching roles. These aren't edge cases — they're the predictable result of a process that depends on human precision under time pressure. And when something goes wrong, the cost is not measured in admin hours but in security incidents.
The Agent
The DevOps Assistant Agent changes the game.
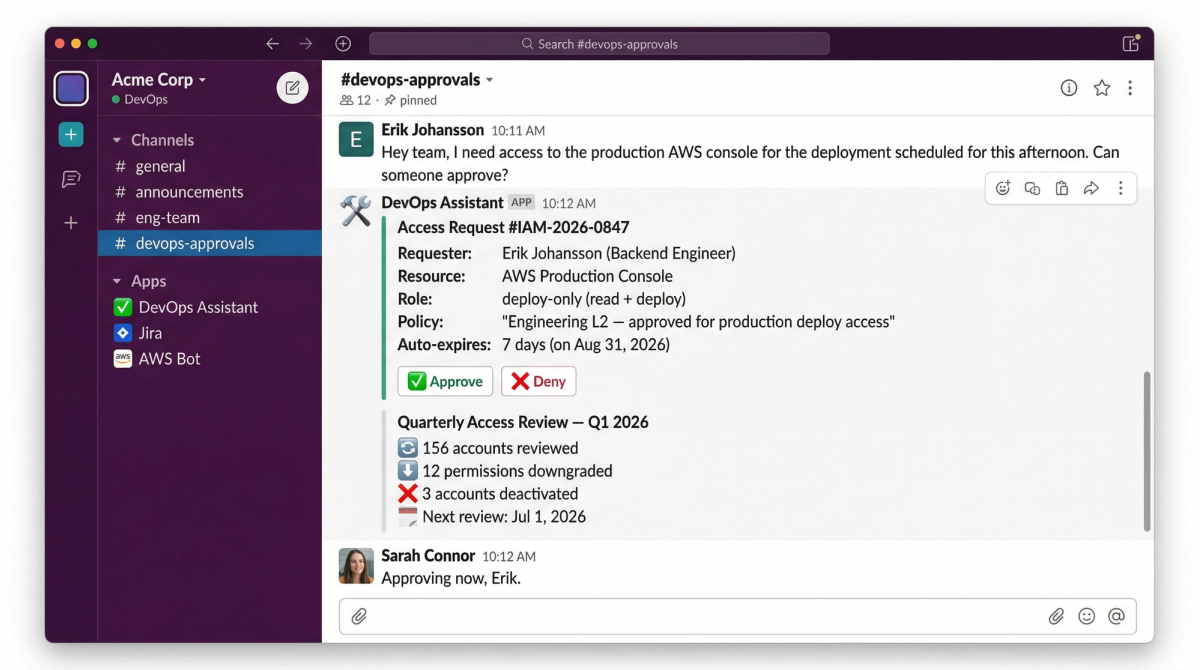
When a new employee needs access — or an existing employee needs a change — an engineer triggers the request in Slack. The agent picks it up, checks the internal access policy documentation to determine the correct permission levels for that person's role, and provisions the access across the relevant systems via the cloud provider API. No console clicking, no cross-referencing policy docs manually, no risk of accidentally granting broader permissions than intended. The request, the policy check, and the provisioning happen in one flow. But the agent doesn't stop at provisioning. On a recurring schedule, it reviews existing access rights across your systems — checking whether permissions still match each employee's current role, flagging accounts that haven't been used, and surfacing access that no longer aligns with policy. Ask it "who still has production access in the data team?" or "which accounts were provisioned more than six months ago and haven't been reviewed?" or "does this engineer's access match their current role?" — and get an answer grounded in your actual policy and current system state.
Every access request provisioned against policy. Every permission reviewed on schedule. No stale accounts. No manual drift.
The agent removes the two biggest risks in access management: the human error that comes from repetitive admin work, and the silent accumulation of permissions that comes from never having time to review.
The Impact
Speed
30+ minutesSaved per access request
Engineers trigger requests in seconds — the agent handles policy checks and provisioning automatically.
Quality Improvement
100%Recurring access reviews with zero manual effort
Permissions stay aligned with roles and policy continuously, not just when someone remembers to check.
But the real win isn't the admin time recovered — it's the reduction in risk. When every access request is checked against policy before it's provisioned, and every existing permission is reviewed on a recurring basis, the gaps that lead to security incidents close before they become problems. Your engineers get their time back, and your access controls actually reflect reality.
Do you want this agent?
Start with a pilot and see how this agent can transform your it ops process in just 4-6 weeks.